BEYOND ONBOARDING: FRAUD PREVENTION IS A CONTINUOUS PROCESS
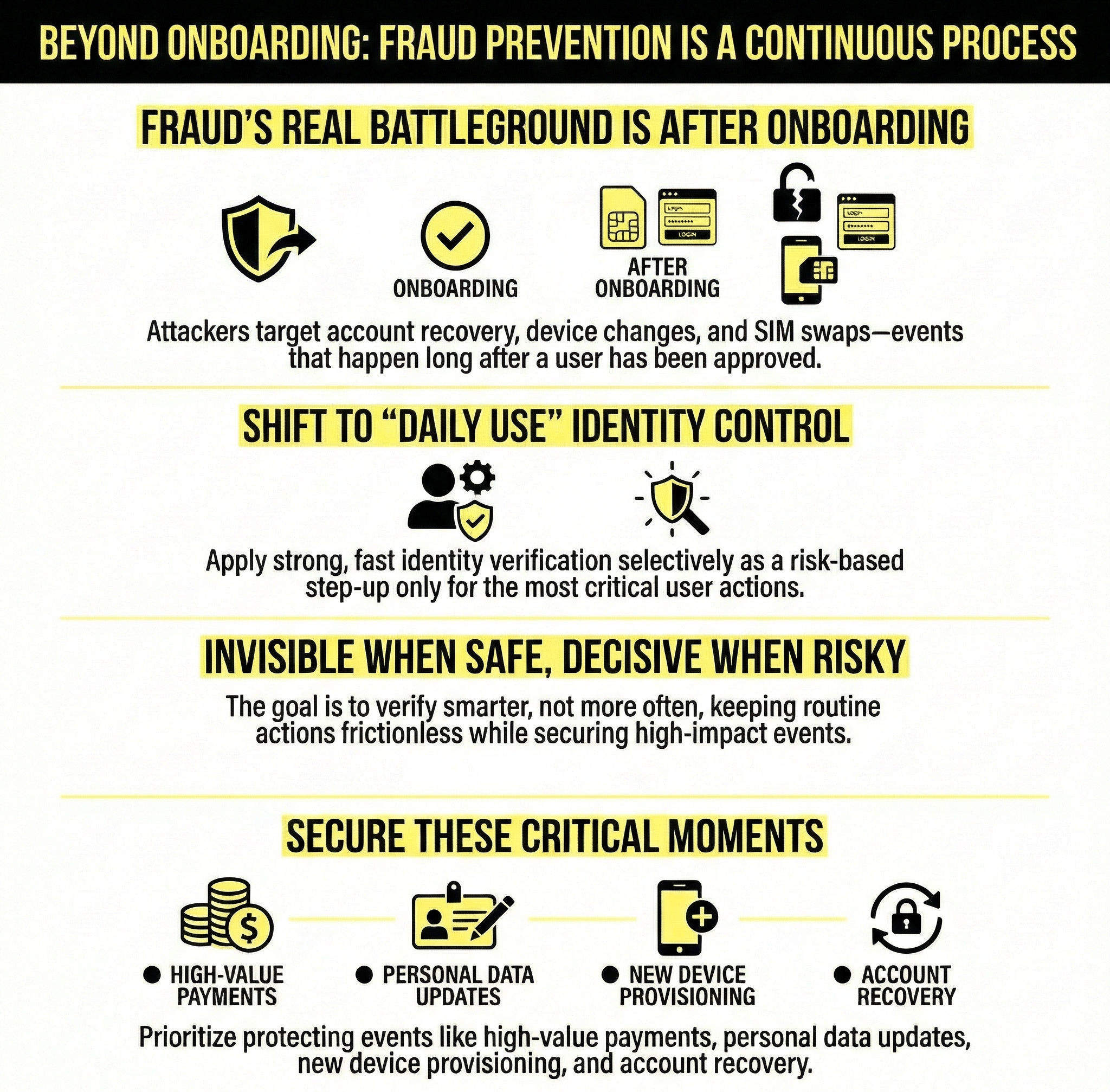
That’s the mindset shift leaders need now: identity is not a moment in time. It’s a control surface. And in modern digital services, control surfaces must be available continuously; quietly, selectively, and embedded inside the journey.
From customer onboarding to everyday identification
Financial services
- approving high-value payments or unusual transfers
- changing payees/beneficiaries or payment limits
- updating personal data (address, phone, email)
- provisioning payment credentials to a new device/wallet
- account recovery (especially when the original device is lost)
Telecom
- SIM/eSIM swap and activation
- number porting (port-out)
- device change tied to account access
- ownership transfer / account takeover recovery
- high-impact profile changes (contact details, authentication factors)
These events share a pattern: they change who can access value. Attackers target them because they often sit outside the “hardened” onboarding flow and rely on weaker methods (SMS codes, knowledge-based checks, or inconsistent call-center processes).
The real battleground: recovery and change events
Account takeover typically follows a predictable chain:
- attacker gains a foothold (phishing, malware, social engineering, leaked credentials)
- attacker triggers a change event (new device, new contact details, SIM swap)
- attacker completes a value event (payment, purchase, payout, data extraction)
If you only validate identity at step 0, you leave steps 2–3 exposed. Daily-use identity is a way to close that gap: bring high-assurance recognition to the events that actually shift control.
Invisible when safe, decisive when risk rises
Daily-use identity succeeds when it acts as a risk-based step-up:
- routine actions remain frictionless
- unusual behavior quietly triggers additional assurance
- high-impact actions require a strong proof of presence
This is also where many programs fail: they apply step-up broadly, creating unnecessary drop-off, customer frustration, and call-center load. A modern approach is to couple identity with risk signals such as:
- new device or browser fingerprint
- new geolocation or network
- anomalous transaction patterns
- change of payee/contact details
- recovery attempts, especially following failed logins
- telecom-specific signals like SIM/eSIM changes or port-out activity
When risk rises, the system asks for a high-assurance, fast confirmation, not another password or a brittle one-time code.
A practical decision framework for leaders
1) Triggering: Where do you step up?
Define the handful of events where assurance must increase. Most organizations don’t need 50 step-ups; they need 5–10 critical ones aligned to fraud and loss drivers.
2) Assurance: How do you prove “the right person is present”?
For everyday use, assurance must be both high-confidence and low-friction. If it blocks legitimate users, it becomes a support problem. If it’s lenient, it becomes a fraud channel. The bar is: fast, consistent, and repeatable, because daily-use identity is invoked often.
3) Fallback: What happens when it fails?
Every high-assurance mechanism needs an escalation path: trusted recovery, customer support workflows, and clear handling of edge cases (camera issues, accessibility needs, device constraints). Fallback design is not an afterthought, it’s part of security.
Embedded identity is the new infrastructure
When identity becomes infrastructure, it becomes:
- always available (for the moments that matter)
- rarely visible (when risk is low)
- consistently auditable (for compliance and incident response)
The direction of travel: recognition becomes normal
How Candour fits this transition?
If you’re currently mapping fraud journeys and deciding where to place high-assurance step-up in 2026, we’re happy to share a reference architecture and discuss which events typically deliver the highest impact.